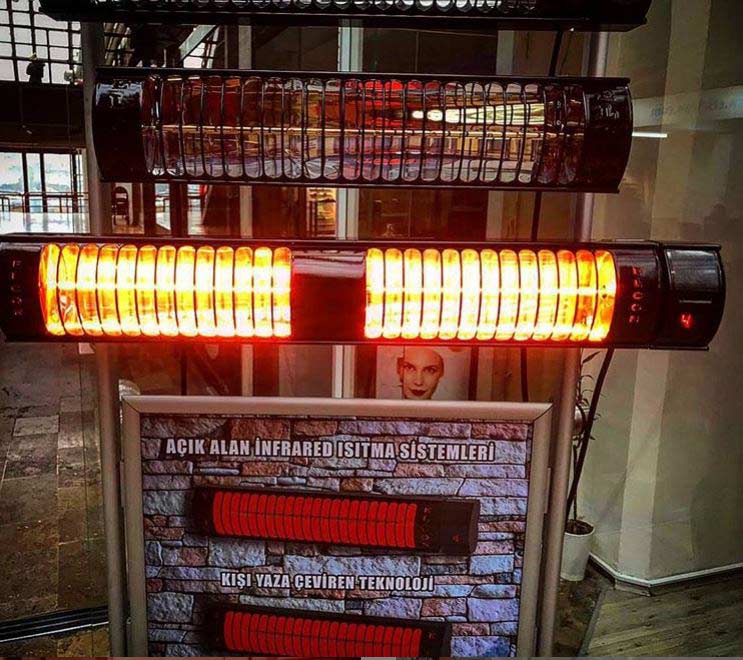
Instalatii climatizare – climatizare de exterior, racire terase, umidificare industriala | panouri radiante si lampi cu infrarosu

Incalzitor terasa, infrarosu, fibra de carbon, telecomanda, 3000W, IP65, de perete/tavan, Scientec + bonus Monitor calitate aer HKE HK-S1 | Incalzitoare de exterior

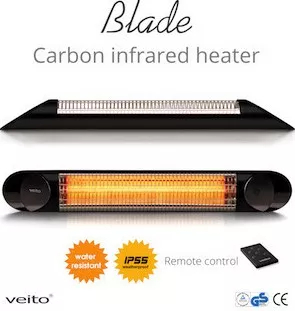
Incalzitor terasa, infrarosu, 2000 W, interior/exterior, IP55, telecomanda, 4 trepte de putere, NEO - Mercaton Store

Veito CH2500RW 2,5kW, Incalzitor electric terasa, Convector electric, Radiator electric, Infrarosu, Interior-Exterior, fibra Car

Incalzitor terasa, tavan, infrarosu, aluminiu, 2000 W, telecomanda, interior/exterior, IP44, NEO - eMAG.ro

Incalzitor terasa, infrarosu, de tavan, 1500 W, telecomanda, interior/ exterior, IP44, NEO - Artool.ro